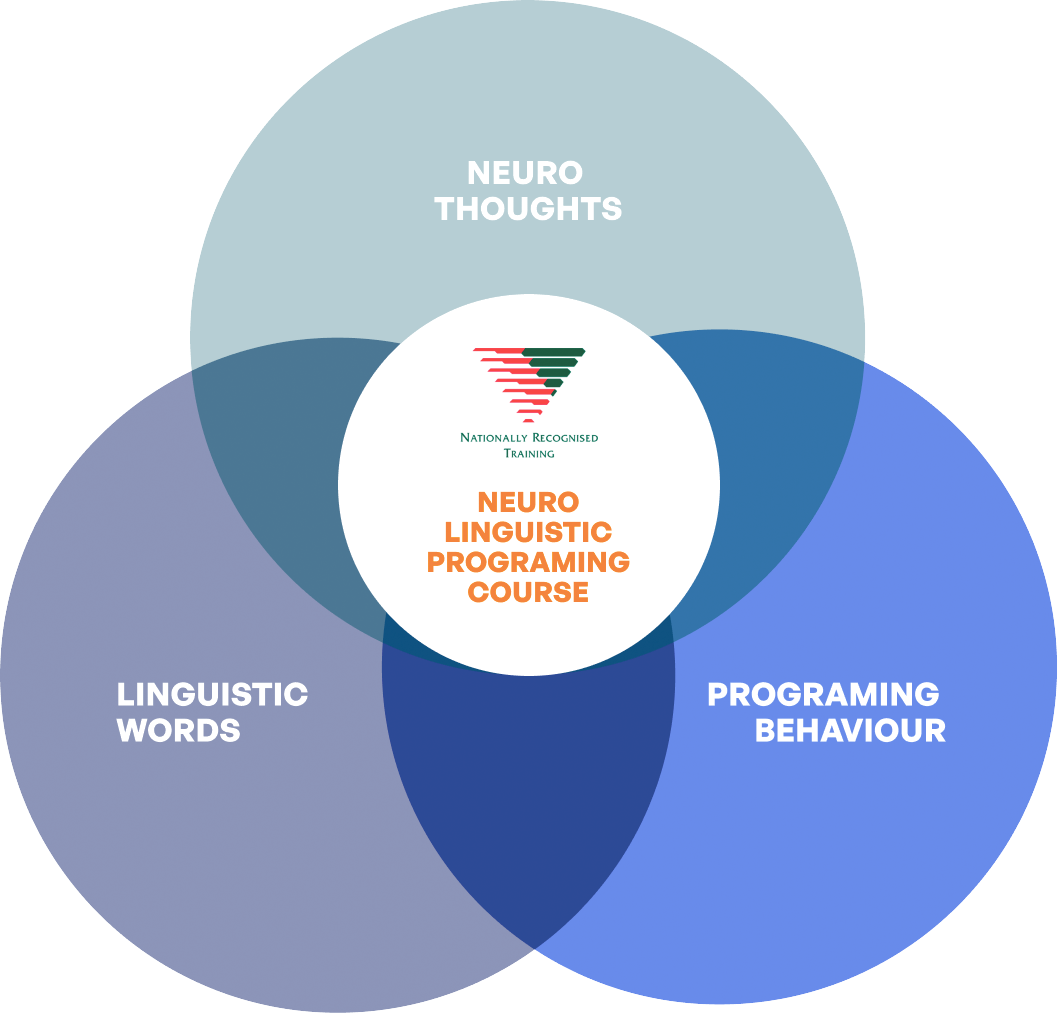
Become Remarkable With Australia's Only Accredited NLP Course
Dedicated to delivering a superior NLP educational journey, we pride ourselves in being Australia's only government-accredited NLP course. Our program is tailored to help you emulate the success of elite achievers, ensuring you become remarkable in life, regardless of your chosen domain.
Inspiritive's NLP mastery is unparalleled, going beyond basic and short-term teachings. While others offer surface-level knowledge, we ensure deep understanding and subconscious application of our patterns, especially in high-pressure scenarios. This is how we’ve helped thousands become the elite 1% that thrives under pressure. Click below to learn more about our 10970NAT Graduate Certificate in Neuro-Linguistic Programming Course.